In Direct mapping, assign each memory block to a specific line in the cache. If a line is previously taken up by a memory block when a new block needs to be loaded, the old block is trashed. An address space is split into two parts index field and a tag field. The cache is used to store the tag field whereas the rest is stored in the main memory. Direct mapping`s performance is directly proportional to the Hit ratio. Show For purposes of cache access, each main memory address can be viewed as consisting of three fields. The least significant w bits identify a unique word or byte within a block of main memory. In most contemporary machines, the address is at the byte level. The remaining s bits specify one of the 2s blocks of main memory. The cache logic interprets these s bits as a tag of s-r bits (most significant portion) and a line field of r bits. This latter field identifies one of the m=2r lines of the cache. In this type of mapping, the associative memory is used to store content and addresses of the memory word. Any block can go into any line of the cache. This means that the word id bits are used to identify which word in the block is needed, but the tag becomes all of the remaining bits. This enables the placement of any word at any place in the cache memory. It is considered to be the fastest and the most flexible mapping form. This form of mapping is an enhanced form of direct mapping where the drawbacks of direct mapping are removed. Set associative addresses the problem of possible thrashing in the direct mapping method. It does this by saying that instead of having exactly one line that a block can map to in the cache, we will group a few lines together creating a set. Then a block in memory can map to any one of the lines of a specific set..Set-associative mapping allows that each word that is present in the cache can have two or more words in the main memory for the same index address. Set associative cache mapping combines the best of direct and associative cache mapping techniques. In this case, the cache consists of a number of sets, each of which consists of a number of lines. The relationships are m = v * k i= j mod v where i=cache set number j=main memory block number v=number of sets m=number of lines in the cache number of sets k=number of lines in each setApplication of Cache Memory –
Types of Locality of reference
GATE Practice Questions – Que-1: A computer has a 256 KByte, 4-way set associative, write back data cache with the block size of 32 Bytes. The processor sends 32-bit addresses to the cache controller. Each cache tag directory entry contains, in addition, to address tag, 2 valid bits, 1 modified bit and 1 replacement bit. The number of bits in the tag field of an address is (A) 11 (B) 14 (C) 16 (D) 27Answer: (C) Explanation: https://www.geeksforgeeks.org/gate-gate-cs-2012-question-54/amp/ Que-2: Consider the data given in previous question. The size of the cache tag directory is (A) 160 Kbits (B) 136 bits (C) 40 Kbits (D) 32 bitsAnswer: (A) Explanation: https://www.geeksforgeeks.org/gate-gate-cs-2012-question-55/amp/ Que-3: An 8KB direct-mapped write-back cache is organized as multiple blocks, each of size 32-bytes. The processor generates 32-bit addresses. The cache controller maintains the tag information for each cache block comprising of the following. 1 Valid bit 1 Modified bitAs many bits as the minimum needed to identify the memory block mapped in the cache. What is the total size of memory needed at the cache controller to store meta-data (tags) for the cache? (A) 4864 bits (B) 6144 bits (C) 6656 bits (D) 5376 bitsAnswer: (D) Explanation: https://www.geeksforgeeks.org/gate-gate-cs-2011-question-43/amp/ Article Contributed by Pooja Taneja and Vaishali Bhatia. Please write comments if you find anything incorrect, or you want to share more information about the topic discussed above.
Please log in or register to add a comment.
Please log in or register to answer this question.
Please log in or register to add a comment.
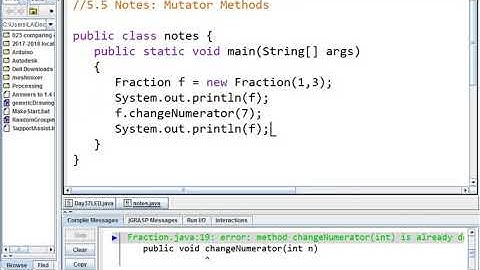
This set of Computer Organization and Architecture Multiple Choice Questions & Answers (MCQs) focuses on “Mapping Functions”. 1. The memory blocks are mapped on to the cache with the help of ______ a) Hash functions b) Vectors c) Mapping functions d) None of the mentioned View Answer Answer: c 2. During a write operation if the required block is not present in the cache then ______ occurs. a) Write latency b) Write hit c) Write delay d) Write miss View Answer Answer: d 3. In ________ protocol the information is directly written into the main memory. a) Write through b) Write back c) Write first d) None of the mentioned View Answer Answer: a
Note: Join free Sanfoundry classes at Telegram or Youtube 4. The only draw back of using the early start protocol is _______ a) Time delay b) Complexity of circuit c) Latency d) High miss rate View Answer Answer: b 5. The method of mapping the consecutive memory blocks to consecutive cache blocks is called ______ a) Set associative b) Associative c) Direct d) Indirect View Answer Answer: c 6. While using the direct mapping technique, in a 16 bit system the higher order 5 bits are used for ________ a) Tag b) Block c) Word d) Id View Answer Answer: a 7. In direct mapping the presence of the block in memory is checked with the help of block field. a) True b) False View Answer Answer: b 8. In associative mapping, in a 16 bit system the tag field has ______ bits. a) 12 b) 8 c) 9 d) 10 View Answer Answer: a 9. The associative mapping is costlier than direct mapping. a) True b) False View Answer Answer: a 10. The technique of searching for a block by going through all the tags is ______ a) Linear search b) Binary search c) Associative search d) None of the mentioned View Answer Answer: c 11. The set-associative map technique is a combination of the direct and associative technique. a) True b) False View Answer Answer: a 12. In set-associative technique, the blocks are grouped into ______ sets. a) 4 b) 8 c) 12 d) 6 View Answer Answer: d 13. A control bit called _________ has to be provided to each block in set-associative. a) Idol bit b) Valid bit c) Reference bit d) All of the mentioned View Answer Answer: b 14. The bit used to indicate whether the block was recently used or not is _______ a) Idol bit b) Control bit c) Reference bit d) Dirty bit View Answer Answer: d 15. Data which is not up-to date is called as _______ a) Spoilt data b) Stale data c) Dirty data d) None of the mentioned View Answer Answer: b Sanfoundry Global Education & Learning Series – Computer Organisation and Architecture. Next Steps:
 Subscribe to his free Masterclasses at Youtube & technical discussions at Telegram SanfoundryClasses. |

zusammenhängende Posts
Werbung
NEUESTEN NACHRICHTEN
Toplisten
#1
#2
#3
Top 8 zeichnen lernen für kinder online 2022
2 Jahrs vor#4
Top 8 schluss machen trotz liebe text 2022
2 Jahrs vor#5
#6
Top 8 wie fallen calvin klein sneaker aus 2022
1 Jahrs vor#7
Top 5 mi band 3 schrittzähler einstellen 2022
1 Jahrs vor#8
#9
Top 9 sich gegenseitig gut tun englisch 2022
2 Jahrs vor#10
Werbung
Populer
Werbung

Urheberrechte © © 2024 wiewird Inc.